Cloud Security Posture Management: Azure Secure Score
Cloud Security Posture Management (CSPM) is the buzz-word these days although relatively new. It comes in different flavors, different tools, all depending on your security needs. CSPM enables you to avoid misconfigurations that can potentially lead to data leakage(s). Before you can do CSPM, you’ll first have to identify your security risks.
The “cloud”, the everchanging biotope, where perpetual changes make it tough to know where your data is stored, makes it even harder for security experts to control and protect data that is moving all the time. How secure is my workload? In comes Azure Security Center, which is in fact a CSPM solution with Secure Score being one of the main features. Some say it is the core of Azure Security Center. But is it?
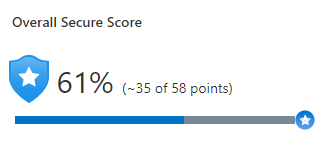
The challenge of most IT departments is not the lack of security tools, but rather knowing where to start their security hardening in their Azure environment. Secure Score is there to help you understand your current security posture, improve the overall security posture and give you a measurement of your workloads’ security over time. You can drill down into your Azure scaffold and go more into detail in your Management Groups and/or Subscriptions to have a more specific Secure Score.
What makes the Secure Score? Secure Score is calculated based on security controls and recommendations. The Secure Score is reevaluated continuously through assessments of your Azure resources that result in security recommendations. Some security recommendations are free, others are a paid Azure service. Whether you choose to follow these security recommendations or not, it will have an impact on your Secure Score but foremost it will leave your vulnerable attack surfaces unprotected.
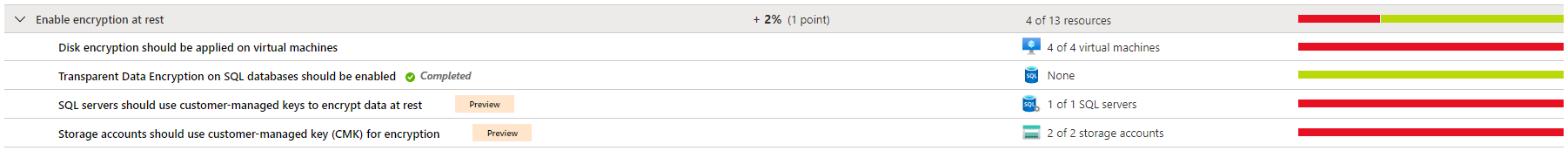
Security recommendations are grouped into Security Controls. They are sourced from the Azure Security Benchmark (ASB). Together with the Cloud Adoption Framework (CAF) they provide strategic guidance, security best practices and multiple reference implementations. Let’s not forget about the Azure Well-Architected framework assessments and the Microsoft Security Best Practices. The Azure Security Benchmark (V2) is built on the Center of Internet Security (CIS) controls.
An example of a security control can be: remediation of vulnerabilities, apply system updates, enable Azure Defender,… When you expand a Security Control, a list of security recommendations is displayed. Most of the security recommendations will give you a brief description, remediation steps, a list of affected resources and a freshness interval. The interval will decide when the security recommendation is reevaluated by Azure Security Center. Patience is of the essence. You also have the ability to exempt one or more security recommendations depending on your company security requirements.
Security recommendations that are in preview are not included in the calculation of your Secure Score.
Our approach is first to look for low hanging fruit, things you can implement without causing too much disruption in your business. Start with enforcing MFA on all of your admin roles, for example. Some security recommendations might have a bigger footprint and perhaps require application owners to revisit their application architecture. These security recommendations will take longer to implement and will probably have a technical and/or business impact. Remember, not all security recommendations will fit your company cloud security posture and some will have a big cost impact. So, from experience, security hardening is weighing off how much security is enough for the customer. And even we, as security experts, are still confronted with the costs that go along with the security hardening.
Obviously, it’s important that IT staff keep revisiting the Secure Score even after they’ve hardened their environment. The security landscape keeps evolving and zero-day attacks remain unpredictable. As does your environment whether it is in Azure or a combination with other clouds or your on-premises datacenter.
One other remark: your Secure Score will be influenced by the amount of resources you allow Azure Security Center to monitor. Awareness and caution are crucial when interpreting your Secure Score.
Engage with a security partner like SecWise, that can translate your Secure Score to your environment and vice versa.